From Iron to Cloud: How Infrastructure as Code Helps Heal Development Pain Points
The transition to Infrastructure as code (IaC) gets faster and changes in the blink of an eye. According to the Global Infrastructure as Code Market Size, Share & Industry Trends Analysis Report, by 2028, the Infrastructure as Code market is expected to reach almost $3 billion. How does IaC happen to show a rising annual growth of 22% in the next couple of years? Why is it crucial for your company’s success? And what development pain points does IaC help heal? Follow us to find the answers!
Infrastructure as Code as an advanced response to the business challenges
In today’s reality, finances, security, speed, and scale are the major challenges businesses face. Poor infrastructure slows innovation, increases risks, and wastes your money. For these reasons, every company must act as fast as possible to build an effective enterprise infrastructure – highly flexible, scalable, and responsive to changes.
Way-way back before Infrastructure as Code emerged, in the Iron Age of IT, a developer wrote an application, and a system administrator got some servers, set them up, configured networking, installed all the necessary software and Databases, and dis all sorts of manual things to make the application run. As a result, a company received extensive resource costs, much effort and time, and a high possibility of human errors.
Nowadays, no one has to do it manually. In the Cloud Age, you just automate the complete process thanks to Infrastructure as Code. If a long time ago, setting up a large number of physical servers would take several hours – now, with a team of IaC professionals, you can have these servers configured and ready to run in just a few seconds. How does it work?
Code rocks, and cloud infrastructure is not an exception
Infrastructure as Code improves the standard of infrastructure management and reduces deployment time. It provides managing data centers, storage, and network infrastructure in a very simple descriptive model. IaC doesn’t require manual setup because configuration data is stored in standardized files. It means you manage your IT infrastructure only with configuration files.
In super simple words, IaC is automating all infrastructure tasks end to end instead of doing it manually. You just pack the knowledge and expertise of system administrators and operations teams into applications to implement all those routines.
Humans do not install new hardware or software systems to support their programs. Everything happens at the code level:
- Developers write the infrastructure specification in a domain-specific language.
- Developers send configuration files to an automation API/server.
- The system creates and configures the resources.
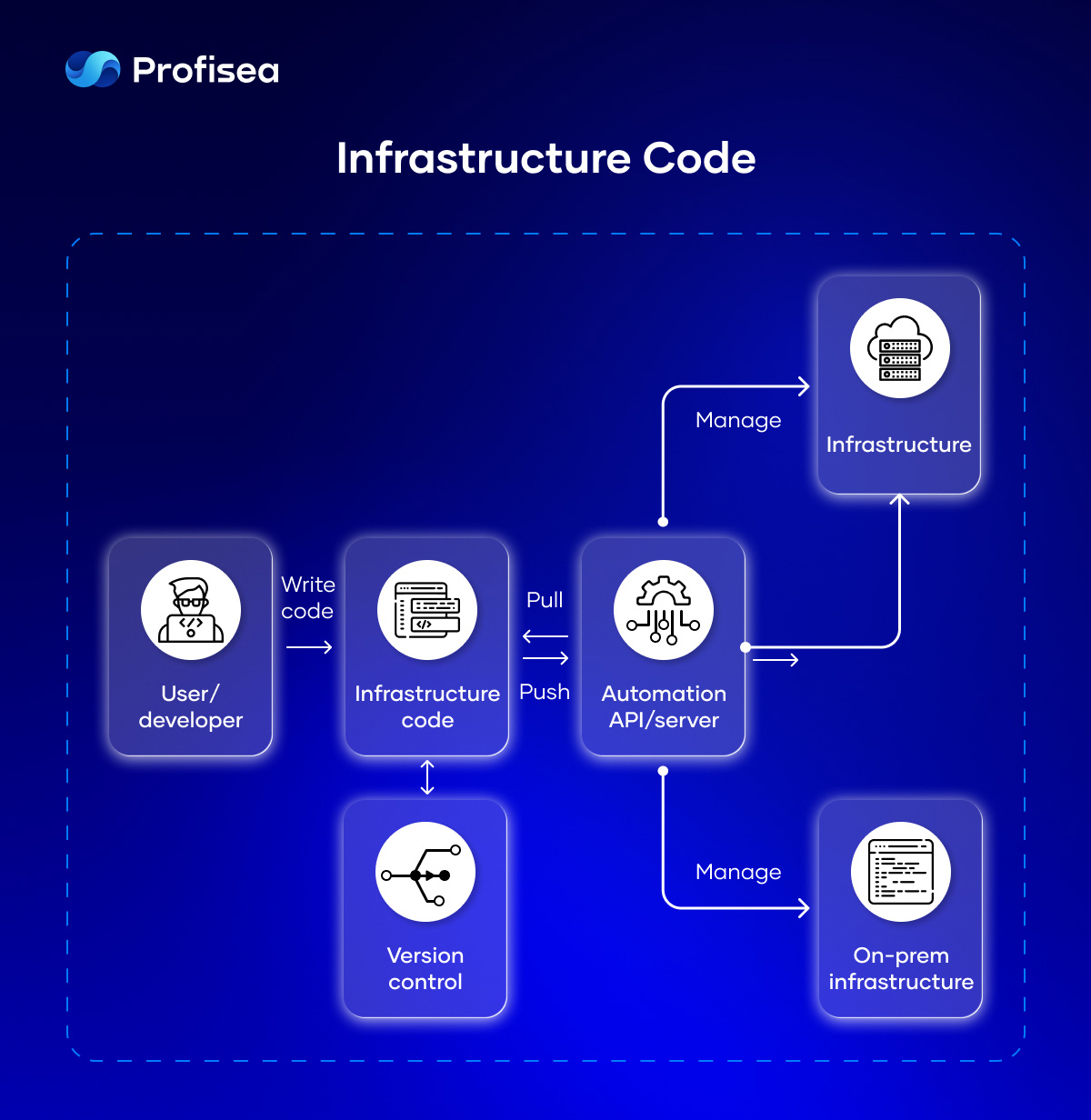
Typically, infrastructure code is managed in the same way as software code, including version control and automated testing. The need for an administrator to log into a new machine and update configurations is substituted by scrips.
In this case, IaC provides the ideal state of the new machine, performing all the necessary configuration steps through the multiple tools: AWS CloudFormation, Azure Resource Manager, Google Cloud Deployment Manager, Terraform, Ansible, Chef, Puppet, Pulumi, etc.
Infrastructure as Code heals development pain points
Keeping your infrastructure in good shape is always difficult. Setting up a new environment can take days and weeks. Unpredictable errors happen during the setup process. IaC heals these development pain points, providing several benefits to the team.
- Speed without loss of quality. As infrastructure is provided with code, it significantly speeds up every phase of the software development life cycle. Therefore, your team can focus on the development and deployment, improving the quality of the software.
- Consistency and portability. With IaC you don’t have to lose sleep over tasks not being completed because of human factors. Consistent configuration without conflicts enables 24/7 rapid infrastructure provision in different environments.
- Version control and traceability. IT specialists version IaC configuration files just like any other source code file. This ensures transparent workflows with tracking of any changes.
- Security and emergency recovery. According to Gartner Report, by 2025, vulnerabilities and misconfigurations will become the reason for 70% of attacks against containers. IaC reduces these risks and helps avoid human errors, runtime problems, and security vulnerabilities caused by configuration drift. Also, IaC is an extremely efficient way to monitor your infrastructure and redeploy it to the last working state after any failure.
- Lower costs. A company saves a lot of money after having eliminated administration, provisioning, and management tasks. Also, well-tuned IaC scripts automatically slow down unnecessary environments to reduce cloud computing costs.

The main thing here is that IaC undergoes the same version control, automated testing, and other continuous integration and continuous delivery (CI/CD) steps just as an application code in SDLC.
Each IaC tool is good in a specific area
AWS CloudFormation, Azure Resource Manager, Google Cloud Deployment Manager, Terraform, Ansible, Chef, Puppet, Pulumi… A very good question is why there are so many different IaC tools. Can’t we just use one that heals everything? Well, currently, no IaC tool can do everything from start to finish. Each tool can do parts of automation tasks, which means each one is good in specific areas.
There are three main categories of automation tasks:
- Infrastructure provisioning, which includes spinning up new servers, doing networking configuration, creating load balancers, etc.
- Infrastructure configuration to prepare the infrastructure/servers with all the necessary software to deploy your app
- Deployment of your application on that provisioned and configured infrastructure
Another important point here is the difference between the initial setup and maintenance phases.
When you provision and configure infrastructure the first time – that is the initial setup. Afterward, at the maintenance phase, you adjust infrastructure, add or remove servers, change network configuration, etc.
Yet again, after the initial installation and configuration of software, you have a software maintenance phase: continuous updates, changes, re-configurations, and so on.
That is why the main difference between all IaC tools is that they automate tasks in different categories for different phases. In most cases, you would use a combination of 2 or more IaC tools to automate the whole process.
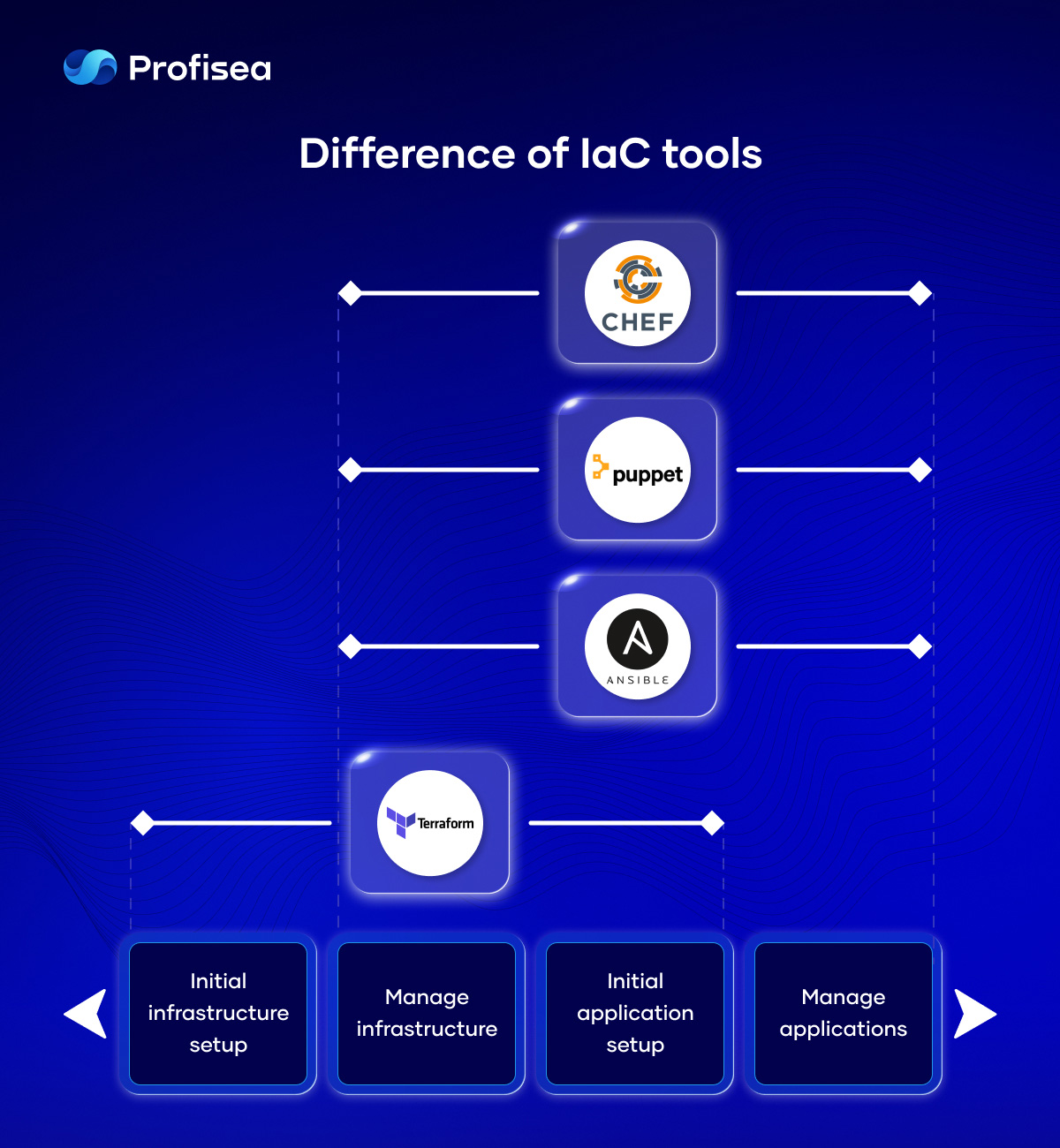
A very common DevOps practice is to use Terraform to provision and configure infrastructure and Ansible – to install and deploy applications on that infrastructure.
Depending on your preferences and needs, there is also a difference between IaC tools in the way they work: declarative or procedural, mutable or immutable infrastructure, agent or agentless, etc.
That is the answer to why we have multiple IaC tools instead of just one.
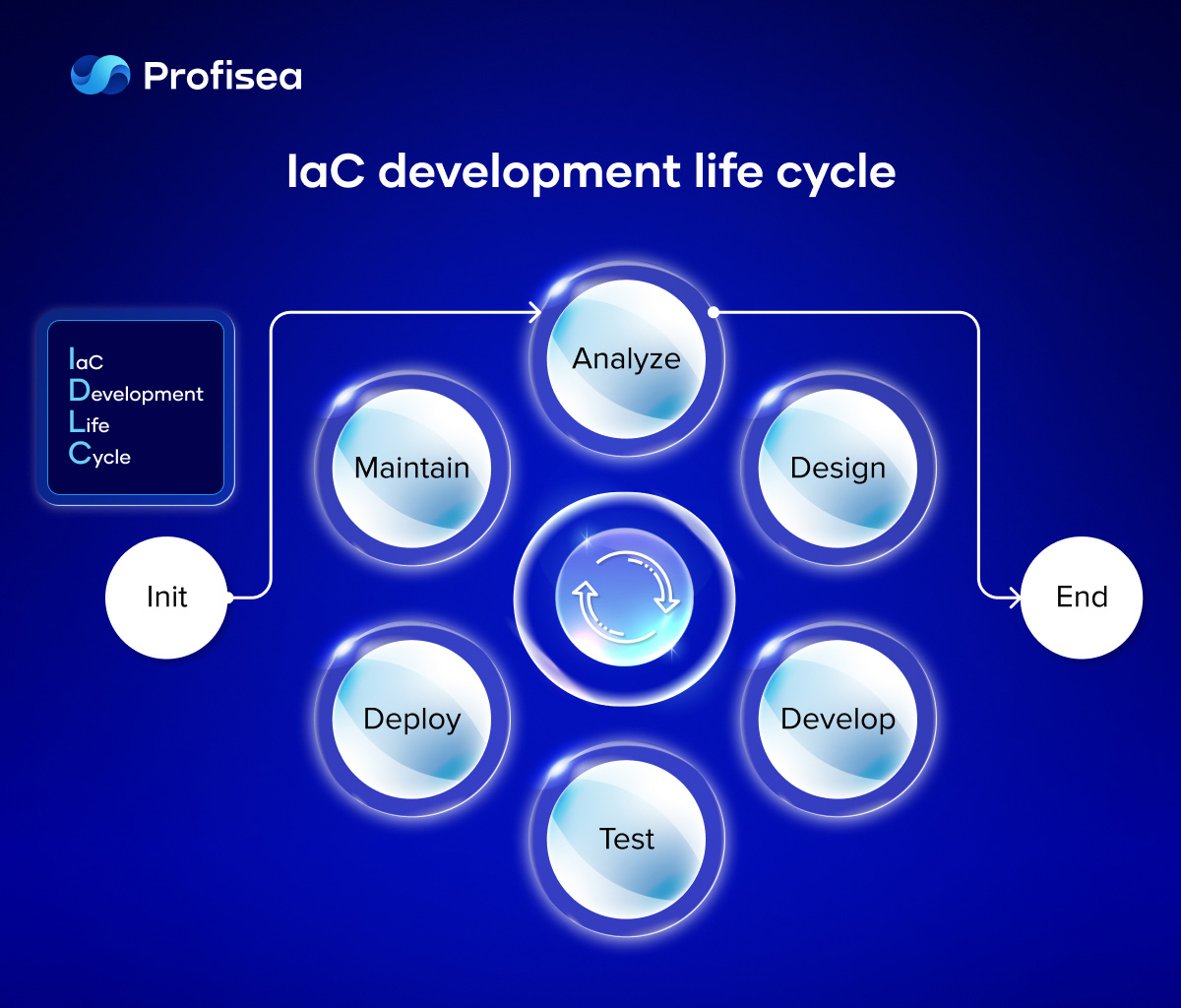
Implementing the IaC approach in SDLC
DevOps relies on Infrastructure as code, that unfolds the full capacity of cloud computing. No doubt, IaC naturally fits the cloud-age business with DevOps tools. But… It’s not the IaC tools that matter – it’s how professionally you use them.
The best practices use a wide range of tools for creating CI/CD pipelines to automatically test and apply the configuration to infrastructure takes much time because you are creating new processes and reversing existing ones.
Let’s put all the IaC implementation steps in SDLC order:
- Preliminary analysis. The main idea here is to understand whether you have enough time and knowledge to make infrastructural changes. If your answer is negative, making changes without involving professional IaC services might be a problem.
- Analysis of the upcoming changes to plan further activities.
- Design. You have the idea to be formalized and to go deeper into details.
- Development. Before writing infrastructure code, you should prepare the IaC development environment using different tools (e.g., Visual Studio Code + Remote-SSH / Vagrant / Ansible).
- IaC Testing includes Static Analysis (ShellCheck, Ansible-lint, YAML Lint), Unit tests (Molecule, Kitchen, Testinfra,inSpec), Integration and E2E tests (Docker + Molecule).
- Deployment (AWS CloudFormation, Azure Resource Manager, Google Cloud Deployment Manager, Terraform,Ansible, Chef, Puppet, Pulumi).
- Maintain. Infrastructure as Code is not static but expected; thus, it’s much easier to maintain infrastructure and implement changes.
To build a reusable, consistent, visible, and versioned infrastructure, you must pass through lots of implementation steps and use a vast number of tools. Without experienced DevOps experts able to design an excellent CI/CD pipeline with all those tools put in the correct sequence, no IaC implementation happens.
Never reinvent the IaC wheel
IaC is much bigger than just plain infrastructure automation. It does require the application of the best DevOps practices to ensure code is error-free, re-deployable on multiple servers, and can be rolled back in case of failure.
Much more productive than hiring in-house, Profisea can benefit your business infrastructure to be agile, flexible, and responsive to market challenges. We provide a full stack of IaC services, including how it is performing, where the performance bottlenecks are, and which errors affect your front-end, back-end, and infrastructure code, etc.
Why don’t you book a free consultation to learn more about top-quality IaC/DevOps services?!